-
The Struts2 scenario that brought down Equifax could really happen anywhere: arstechnica.com/information-technology/2017/09/massive-equifax-breach-caused-by-failure-to-patch-two-month-old-bug/
-
"The flaw in the Apache Struts framework was fixed on March 6. Three days later, the bug was already under mass attack"
-
Companies have very little time to react. Especially hard at very large organizations with hundreds of legacy production applications
-
The scenario affecting Struts2 can easily be applied to Spring/Grails/Play/etc... All have routine patches to fix vulnerabilities
-
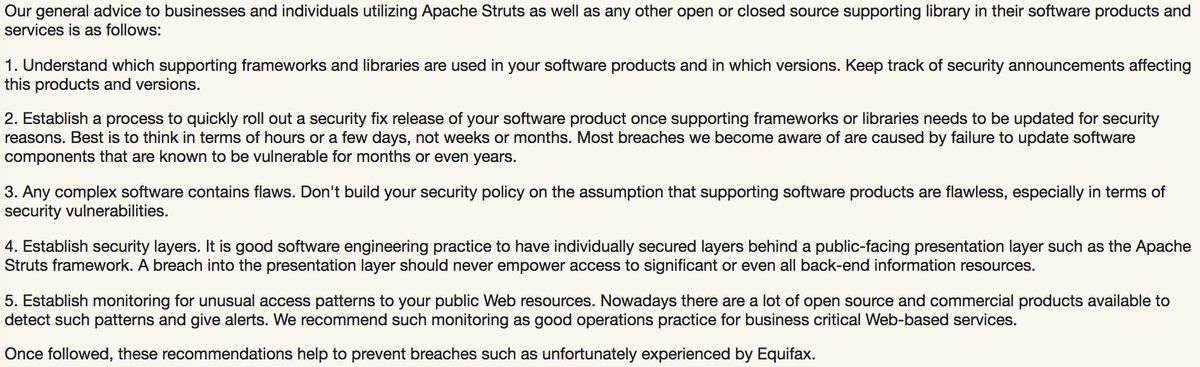
The key is to have processes and procedures in place to quickly rebuild and redeploy and regression test applications
-
But also to internally rank applications on level of criticality and priority for updates
-
e.g. A grocery store list app -- low priority. A stock trading app -- pretty critical.
-
there are tools to help - starting with a dependency tracking tool like Artifactory or Nexus to have an inventory libraries
-
implementing a continuous delivery/integration pipeline should also be at the top of your list
-
and major props to @TheApacheStruts for being open and quick in their response @TheASF/908284325044436992
-
@TheApacheStruts Great writeup on how the issue isn't OS tools. Open Source is actually what helps to patch these holes faster blogs.apache.org/foundation/entry/apache-struts-statement-on-equifax
-
@TheApacheStruts "there is a huge difference between detecting a flaw after nine years and knowing about a flaw for several years"
-
Look at @VersionEye and jeremylong.github.io/DependencyCheck/ as tools to auto-scan and notify for vulnerable libraries on your projects
-
It’s not easy, but quick detection & notification, fast patching, auto regression tests, and timely deploys are the new norm
-
To be clear - this applies to Node, Ruby, C#, Python, just as much as Java. Security holes happen. So we must plan for them.
-
Adding two more security scanning / checking tools to the thread: @black_duck_sw and @Checkmarx